Security Week 52: Hacking Reddit, A Purse For Cryptocurrency And MikroTik Routers
There was no news last week about the infobase, worthy of a detailed description in the digest. This does not mean that nothing happened – this situation, it seems, is completely impossible. Someone who was not hacked. Well, as compensation for the previous opus about the theoretical network Specter-like attack today we will talk about two real attacks and one circus with horses with the participation of John McAfee.
Reddit was hacked simply. Reddit as a rather specific community, and, moreover, very popular, for sure is subjected to absolutely all possible types of cyber attacks and in fact, is rather well protected. This conclusion can be drawn both from an absolutely honest story about the recent successful attack and from the fact that in the past such stories did not seem to exist. The attack was complicated, but it was easy to describe the reason for successful hacking: two-factor authentication was bypassed.
- Reddit laid out a detailed description of the incident (Captain!) On Reddit. Here you can read the retelling in Russian. The employees of the company became aware of the attack on June 19. From 14 to 18 June, attackers had partial access to the internal infrastructure of the organization, hacking several accounts of employees. All accounts that have access to important information were protected by the 2FA system, but it was circumvented by “intercepting SMS.”
Details of this interception are not disclosed, although in a note on the Wired site it was assumed that there was a duplicate SIM card issue. Such an attack could be detected and quickly, especially if several accounts were stolen. Either way, crackers got partial access to cloud storage. There they accessed the database with logins, addresses and hashed with passwords from Reddit users until 2007 (Reddit was launched in 2005). There were also stored all user messages, including private messages, but only for the first two years of the site’s existence.
Thus, the early Reddit users suffered most. In addition, access to the logs of the mail server was obtained. From them, you can find out who received the mailing list of the site from 3 to 17 June 2018. The problem is that these logs can be associated with a username on Reddit with a mail address: this information can be used later – for example, for phishing attacks. What was done? Measures have been taken to prevent re-attack, including the transition to two-factor authentication using physical tokens. It is thanks to authorization using tokens from the beginning of 2017 that Google has not detected any successful phishing attacks.

In April of this year, MikroTik routers detected and closed the zero-day vulnerability. An error in the implementation of the Winbox remote management system made it possible to extract a user database in which there was enough information to gain full control over the router. Vulnerability at that time was already exploited by intruders, but the scale of the attack was small. The patch covering the problem was released within a day, but everyone knows how quickly the owners of routers, even professional ones, update the software.
Last week, the BleepingComputer site collected information from three different sources and counted up to two hundred thousand Mikrotik routers compromised with the help of the April vulnerability and embedded the Coinhive cryptocurrency code into web pages. That is, all users connected to a hacked router are starting to lease their computing power for leasing for mining. The attack works in both directions: if a website is behind the router, its visitors also receive a harmful load in the site code. In some cases, the code of the miner was not inserted into all web pages, but only in those generated by the router itself, for example, messages about access to the site. IoT-search engine Shodan indexes 1.7 million Mikrotik routers visible from the network. Based on this figure, we can note both a sufficiently serious share of the already infected devices and opportunities for expanding the crypto-currency botnet.
The saga of a non-crash purse for cryptocurrency

Okay, this is not a saga, it’s more of an anecdote. Any sphere of the national economy becomes more fun if John McAfee is involved in it. July 27, the founder of McAfee Security, recently shifted all his attention from the Infosecurity to crypto-currencies, announced a $ 100,000 reward for hacking the Bitfi crypto-currency wallet.
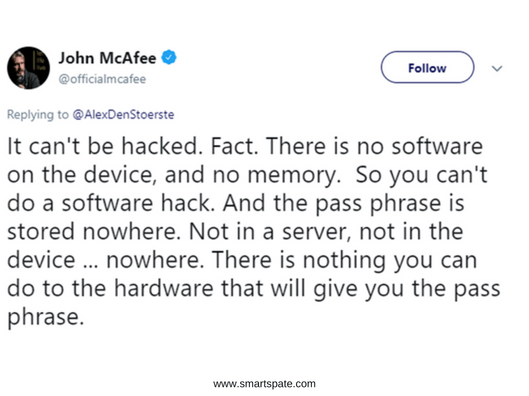
The Bitfi wallet is advertised as absolutely safe, but also a convenient device for storing and working with the keys to access to the cryptocurrency. And John McAfee himself actively promotes Bitfi as an absolutely unbreakable device, hence the reward. McAfee statement caused, let’s say, an increased frustration from the community of security experts – for two reasons. First, to say that something cannot be hacked – move on. Secondly, the terms suggested by the manufacturer of the Bitfi wallets are far from the standard Bug Bounty program. Participants are invited to buy Bitfi with a “key” on it, giving access to money. If this key can be stolen, the “stolen” cryptocurrency is supposed to be used as a reward, and one hundred thousand dollars from above.
But real security is not to blame! You can encrypt data, put them on a USB flash drive, and without a key, no one decrypts them. The bottom line is how reliably the device works in practice when access to sensitive data occurs. Is it possible to intercept a secret during transmission? Can I steal a pin to access my wallet? In theory, we must answer the question of how the device will work in real conditions, and not how well it will be encoded crypto money.

Not that John McAfee and Bitfi as a whole stopped this. A couple of days after the announcement, the reward for breaking the wallet was raised to 250 thousand dollars while preserving the conditions. BitTor’s Twitter account blamed them for their competitors’ work on the claims of researchers from PenTestPartners. In response, PenTestPartners bought the device and disassembled it. Inside, a slightly truncated MediaTek smartphone platform with a modified Android was found, with all the built-in “almost” backdoors typical for a cheap Chinese smartphone. When an independent Dutch researcher found a fairly simple way to get superuser rights on the device, the question of purse security could be considered closed. But Bitfi did not give up:
- Then we have a device that does not have software and memory. The rights of the rue do not allow you to crack the wallet. We must give credit: at some point, Twitter Bitfi apologized for the behavior of one of its employees responsible for tweets, stopped responding to all the template “the fool himself,” but it did not get better from this. At the time of publication, the story continues to evolve: the researchers dismantle the crypto and find new problems, Bitfi and McAfee ride around in a hip-hop car.
All this, of course, is incredibly funny, if it were not a little sad from lowering the quality of the discussion about security to the level of a rural disco. The norms of device security, from crypto tices to smart locks and cars, are not particularly defined by anyone. Although the majority of those who are related to the info basement observe the rules of propriety, sometimes such “unbreakable” wallets, “super-reliable” locks and other fruits of marketing fantasies appear. However, reality usually puts everything in its place.





