Hacking Google Home And Amazon Echo To Protect Privacy!
Security experts are skeptical about the concepts of “smart home” and “Internet of things”. Manufacturers strive to collect more data about users, which is fraught with leaks. Amazon recently sent 1700 conversations from a single user with Alexa’s home assistant to the wrong address.
This is an isolated case, but Amazon keeps audio recordings on its servers, just like Google. A home assistant like Amazon Echo and Google Home is a full-fledged bug that the user himself installs in the house, voluntarily agreeing to wiretap. So far, there is no evidence that such devices record without uttering a trigger word, but technically nothing prevents them from doing so.
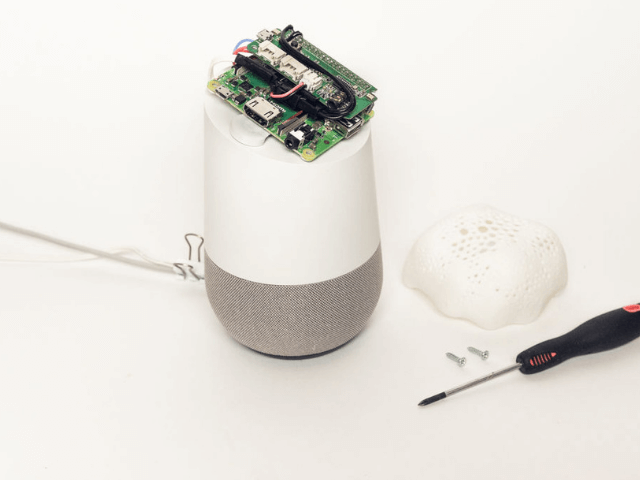
Project Alias is designed to change things and bring back control to people.
Project Alias is the technological equivalent of a parasitic fungus that lives on a foreign body. And this is a very useful “parasite“ because it acts as a protector for its true owner, that is, man. Alias blocks the transfer of information to the corporations Amazon and Google, drowning out the microphones of the host.

The assembly instructions are published on the Instructables website, and the program code is posted on Github.
To install will need:
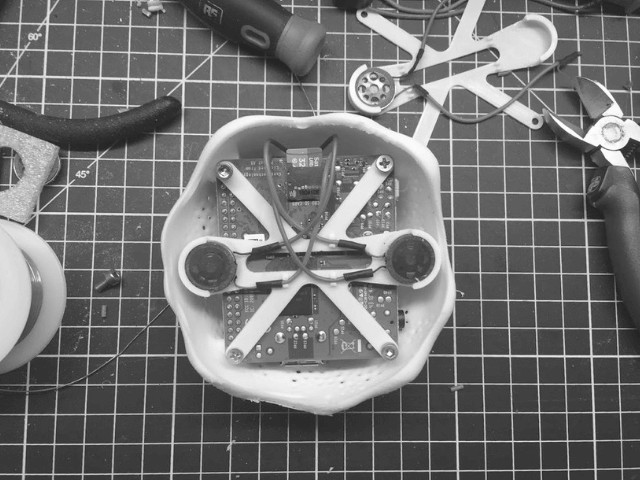
- A single-board computer with the Raspbian operating system, Raspberry Pi A + is sufficient;
- ReSpeaker 2-Mics Pi HAT plug-in with microphones;
- Tiny Speaker 16mm speakers;
- Micro SD card, audio cable, wires, and four screws;
- Access to a 3D printer for printing the cover and holder.

The network has published 3D models of covers for Google Home (stl) and Amazon Echo (stl), as well as a 3D model of the speaker holder (stl).
The next step is to build Alias. It includes connecting speakers to the ReSpeaker module and connecting the 5V power supply to the Raspberry Pi (solder directly on the GPIO).

After the assembly, the software begins:
1) Download the latest version of Raspbian on micro SD.
Copy the files ssh and wpa_supplicant.conf from the project folder, edit the latter according to your WiFi settings.
2) Install sound driver for ReSpeaker.
cd && git clone https://github.com/respeaker/seeed-voicecard.git cd seeed-voicecard && sudo ./install.sh
3) Install Tensorflow and Keras.
sudo apt-get install python3-dev python3-pip git libatlas-base-dev sudo pip3 install tensorflow keras
4) Install the remaining required modules.
sudo apt-get install python3-numpy python3-spidev python-h5py sudo apt-get install python3-pyaudio libsdl-ttf2.0-0 python3-pygame sudo pip3 install flask flask_socketio python_speech_features
5) Clone the Alias project.
git <span class="hljs-built_in">clone</span> https://github.com/bjoernkarmann/project_alias.git
6) Install the boot script and reload the Raspberry Pi.

Then you need to train Alias to recognize your name, it can be arbitrary (any sound is less than 2 s). The developers write that it is enough 4–6 times to write the name on the phone and press the Train Alias button.
If desired, then the name can be changed.
And it’s all. In the future, Raspberry Pi performs speech recognition itself, and the voice assistant no longer responds to the standard name (for example, Alex) and does not send any data to the Google/Amazon cloud.

The authors of the project are Danish developers Bjorn Karmann and Tore Knudsen.
Manufacturers of such gadgets consider the buyer simply a user of the product and not the true owner. Perhaps they will try, through lawyers, to ban the modification of gadgets, considering them to be their intellectual property. But according to the laws of many countries, the purchased product becomes the full property of the buyer, and he has the right to do anything with it.





