Security Weekly 41: Fuss Around Facebook, The Popularity Of Extortionists, Patches Specter
A broad discussion of the privacy of user data on Facebook is a more public topic, and if you try to find any technical features in it, it turns out that nothing has happened to Facebook over the past month. Unless the developers of the Firefox browser in late March released a solution that allows you to isolate the Facebook user account from other activity on the web.
And otherwise, as usual: the journalists will dig up even more shocking details about the leakage of data, then Tim Cook from Apple comments on the topic “we sell products to users, not users to advertisers”, then Mark Zuckerberg will respond that “everything is not so unambiguous.” The technical community is mostly surprised: what’s new? It has long been clear that any public activity on the Internet will be analyzed by someone and, perhaps, somehow used – for the benefit of users or how it will turn out.
Far from always processing large data is a must. The question is how to make this process more transparent.

Following the hearings in the American Congress with the participation of the CEO of Facebook, the English-language Threatpost publishes a detailed description of possible legislative initiatives that pursue the goal of more transparency in the collection and transfer of personal data. And in the same US, there is already a definition of the Federal Trade Commission that social networks should ask permission of the user if they want to pass information about him to a third party. So they warn, but who reads these warnings? To the conventionally idle designs, it is possible to refer both the initiative Do Not Track, and the European law Cookie Law.
It is obvious that there will be more initiatives on the background of the bustle around Facebook, and, possibly, large data operators will become more compliant. Despite the powerful news background, this problem will be solved by political methods for a long time, there it is always so. Technology for replacing the existing status quo is also not expected unless some decentralized social Internet with a thick layer of the blockade. Type Diaspora, but better. Much, much better.
Almost 40% of cyber attacks on business are accounted for by Trojan coders
The Verizon telecommunications company’s report on threats to business is built out of the box. Companies in the sample total 67 (they represent 65 countries), but each, apparently, provided detailed information on incidents for the year. In total, 53,000 incidents and 2,216 successful attacks were analyzed – English breaches can be interpreted as both data leakage and as an attacker gaining control over part of the corporate infrastructure. 39% of successful attacks using the malicious software in one way or another refers to infection by the Trojan-encryptor. Verizon notes that the complexity and scale of attacks are growing: under the impact are not only workstations but also – increasingly – file servers. The reason is clear – the more data “taken prisoner”, the greater the potential ransom.
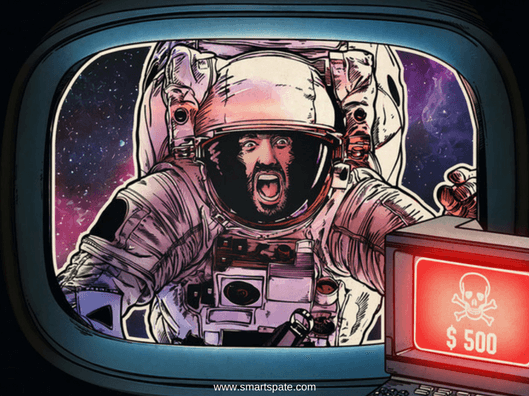
A few more interesting facts from the study. E-mail remains the main way of penetration. Phishing, sending malware under the guise of financial documents – depending on the method of counting up to 93% of successful attacks, it is precisely these tools. It can be concluded that the malware industry is rapidly monetizing. For the development of this criminal business, it is not even necessary to use the latest methods of hacking.
- For example, Kryptos Logic reports on 2.7 million computers still infected with the WannaCry encryptor. This attack was at least unconventional, but it happened almost a year ago, it was immediately stopped and since then, it would seem, should be stopped without any problems. Despite this, in March, the incident related to WannaCry, occurred in the network of the company Boeing, and as we see, millions of computers are still infected with this trojan.
One line
AMD releases patches to protect against Specter’s vulnerability. The patches are relevant for processors released since 2011, but microcode updates are not enough: the vulnerability can only be completely closed in combination with the latest version of Windows (an update for Windows 10 is also released this week) or with the current Linux kernel, the patch for which already is available for a while.
The April release of patches from Microsoft eliminates 66 vulnerabilities, including 24 critical ones. Among them is the XSS vulnerability in the Sharepoint server, which allows increasing privileges slightly.
- If someone else uses Adobe Flash Player, it also closed a couple of holes.
Schneider Electric has released patches for industrial systems, including a serious vulnerability that allows intercepting control remotely. The set of problems is no different from that for a home computer: vulnerability in Samba, SQL injection and the like.





