Why is Mozilla Called One Of The Villains Of Internet Browsers?
In early July, the UK Internet Service Providers Association (ISPA-UK) summed up the annual nomination “main character” and “main villain” of the Internet. Among the “main villains” organization Mozilla hit.
This is an unexpected decision. The Manifesto and 10 principles are widely known, according to which Mozilla promises to fight for the health of the Internet: “The open, global Internet is the most powerful communication and collaboration resources known to us. He embodies our deepest hopes for human progress. It provides new opportunities for learning, understanding and solving global problems. ”
Mozilla – one of the few organizations that aims not to make a profit, namely the development of the Internet and the protection of users. Why was she awarded the title of “main villain”? It turns out that it is for this, that is, for the “excessive” protection of users. DoH (DNS-over-HTTPS) became the bone of contention.
- According to the ISPA-UK wording, Mozilla won the title of “Internet villain” “for their proposed approach to implementing DNS-over-HTTPS in such a way as to circumvent the UK filtering and parental control obligations, undermining the UK’s Internet security standards.
Pay attention to the phrase “undermining safety standards.”
DNS-over-HTTPS
Mozilla did participate in the development of DNS-over-HTTPS, which was subsequently designed as an IETF standard.
“We are concerned about companies and organizations that secretly collect and sell user data. Therefore, we added protection against tracking, ”wrote Lin Clark on behalf of Mozilla shortly after the adoption of the standard. “These two initiatives (+ Trusted Recursive Resolver) eliminate data leaks that have been part of the domain name system since its inception 35 years ago.”
Lin Clark explains how an insecure DNS system endangers users:
Usually the resolver tells each DNS server which domain you are looking for. This request sometimes includes your full IP address. And if not the full address, then increasingly, the request includes most of your IP address, which can be easily combined with other information to establish your identity.
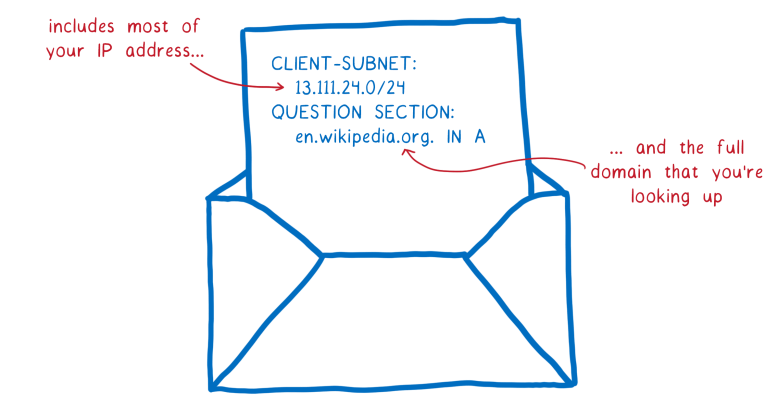
This means that every server you ask for help with resolving domain names sees which site you are looking for. Moreover, anyone on the way to these servers also sees your requests. There are several ways in which such a system compromises user data. The two main ones are tracking (tracking) and spoofing (spoofing).
With full or partial information about an IP address, it is easy to determine the identity of someone who requests access to a particular site. This means that the DNS server and any user on the way to this DNS server (router on the way) can create a user profile. They can make a list of all the sites you have viewed.
And this is valuable data. Many people and companies are willing to pay a lot to see your browsing history.
Here the question arises: who is “on the way to this DNS server” and “can create a user profile”, which can then be sold to third parties?
This is your internet provider.
- Perhaps one should not take seriously the argument that “DNS-over-HTTPS allows you to bypass the UK filtering and parental control obligations, undermining the standards of Internet security in the UK”, and the discontent of Internet providers is much easier to explain: lost profits.
There is another version: “In fact, everything is simple,” writes Russian expert Mikhail Klimariev, executive director of the Internet Protection Society. – The UK Providers Association has been fighting against blocking for a long time. In the end, they agreed with the government that the blocking would be done “by DNS”. That is, without any DPI and “by IP“. That is why Mozilla is a villain. For blocking by DNS will be useless. More precisely – everyone knew about it before, and Mozilla publicly stated that now all this is useless. And now the members of the Association will have to renegotiate somehow. Or take lessons from the ILV. That is why Mozilla is the “villains”. ”
The encryption of DNS traffic over HTTPS has already been implemented by a number of public DNS providers, including Cloudflare (1.1.1.1, 1.0.0.1) and Google Public DNS (8.8.8.8, 8.8.4.4).
Personal privacy or public safety
In general, the wording of ISPA-UK assumes that the introduction of encryption and reliable privacy threatens the user’s security, because the state “defender” will not be able to protect him. In this case, DNS-over-HTTPS prevents providers from filtering harmful content. This logic contrasts privacy and security.
- Personal privacy can really be opposed to public safety. Now there are discussions about what is more important and in which direction to shift the accents. For example, the authorities of some countries are inclined to prohibit end-to-end encryption in all instant messengers altogether. Some governments introduce forced filtering of traffic, limiting public access to a specific list of sites, as in the UK.
Proponents of the opposite concept of personal privacy point to the proliferation of surveillance that threatens a person’s normal life in the long run. The same is said in the Mozilla Manifesto, where Principle No. 4 states: “The security and privacy of Internet users are fundamental and cannot be considered as secondary moments.”
Refusing to encrypt, a person actually refuses his own protection and his digital assets are available not only to the state, but also to attackers. This is well illustrated by the example of DNS-over-HTTPS, which protects against MiTM attacks, including with page spoofing. So, encrypting traffic and protection from surveillance on the Internet is not a matter of choice, but a matter of survival in the future technological society, supporters of personal privacy say.
On the side of state authorities is an administrative resource. But on the other hand, they are opposed to technological progress. The discussion continues.





