Web Hosting Firm Shells Out $1M in Yet Another Linux-Targeting Ransomware
On June 10, the South Korean hosting company NAYANA became a victim of the attack of the extortion virus Erebus (detected by Trend Micro as RANSOM_ELFEREBUS.A). As a result, 153 Linux servers and more than 3400 business websites hosted by the hosting provider were infected.
In a message posted on NAYANA’s website on June 12, the company said that the attackers demanded an unprecedented 550-bitcoin (BTC) buy-out or 1.62 million dollars for decrypting files on all infected servers.
Here is part of the negotiations with extortionists:
My boss told me to give you a good price since you buy a lot of cars,
550 BTC
If you do not have enough money, you need to take a loanYou have 40 employees,
The annual salary of each employee is $ 30,000
All employees 30 000 * 40 = $ 1 200 000
All servers 550BTC = $ 1,620,000If you can not pay, you are bankrupt.
You will have to face your children, your wife, clients, and employees.
Also, you will lose your reputation and business.
You will receive many lawsuits.
Later on June 14, NAYANA announced an arrangement for the payment by installments of 397.6 BTC (about 1.01 million US dollars as of June 19, 2017). June 17, the company said that the second of three payments was made. On June 18, NAYANA started restoring the server in batches. Currently, some servers of the second batch have database errors. The third payment will be paid after the successful restoration of the first and second batch of servers.
- Although this is not comparable in terms of foreclosure, the case resembles what happened to the hospital in Kansas, whose employees did not have full access to the encrypted files after payment. Instead, the extortionist demanded a ransom again.
Erebus was first seen in September 2016, then it was distributed through malicious advertising. Again, it appeared in February 2017, already using a method that bypassed the Windows account control.
Here are some of the technical details that are available about the Linux version of Erebus:
Possible vector of virus attacks
As to how Linux systems are infected, we can only assume that Erebus may have used the Linux exploit. For example, based on open source information, researchers found that the NAYANA site runs on Linux 2.6.24.2, which was compiled in 2008. Therefore, security threats, such as DIRTY COW, can give root keeper root access to vulnerable Linux systems.
In addition, the NAYANA website uses legacy versions of Apache 1.3.36 and PHP 5.1.4, both of which were released as early as 2006. The version of Apache used by NAYANA runs under user nobody (UID = 99), which indicates that some previously known exploits could also be used in the attack.
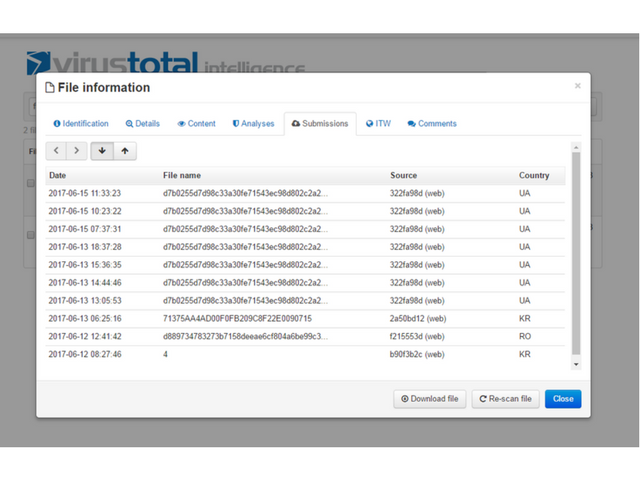
It should be noted that this extortion virus is limited in geographic coverage and, in fact, attacks are concentrated in South Korea. However, the VirusTotal service data show otherwise – several samples were also received from Ukraine and Romania. A possible reason may be that they were sent by other researchers in the field of information security.
Encryption procedure
Each file encrypted with Erebus will have the following format:

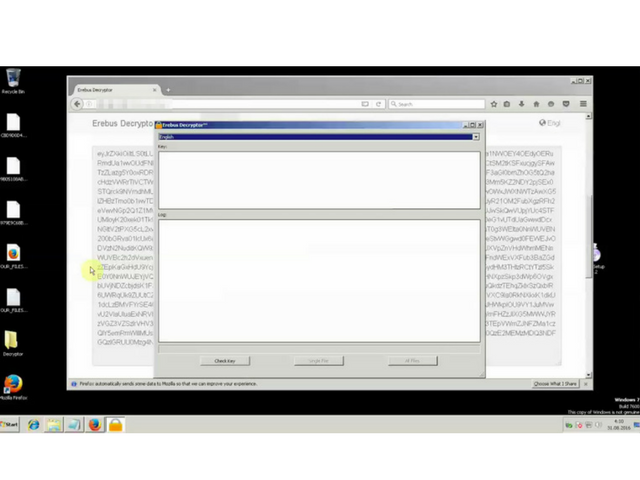
First, each separate file is divided into 500 kB blocks and scrambled using the RC4 encryption algorithm with randomly generated keys. The RC4 key is then encoded by the AES encryption algorithm. The AES key is again encrypted using the RSA-2048 algorithm, the public key of which is stored in the file.
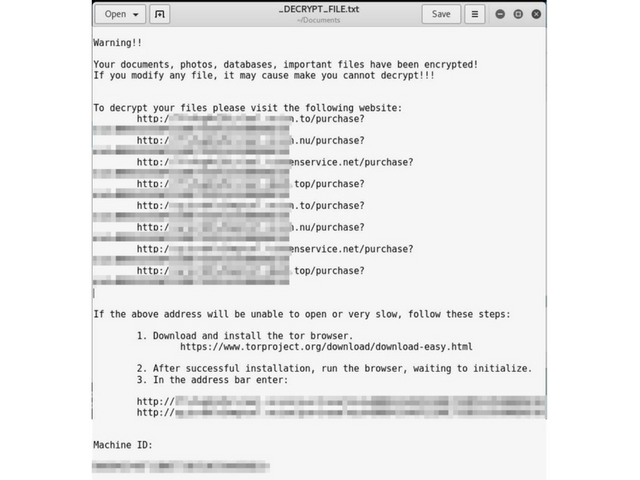
Each file has one RSA-2048 public key common to all. RSA-2048 keys are generated locally, and the private key required for decryption is stored in the encrypted one using an additional randomly generated (possibly including on the basis of Machine ID) AES-key. The analysis shows that decryption is impossible without obtaining RSA-keys.
File Target Types
Usually, encryption is aimed at office documents, databases, archives and multimedia files. This is also true for this version of Erebus, which encrypts 433 file types but also seeks to encrypt Web servers and data stored on them.
The table below shows the folders that Erebus is looking for.
Var/www / – folders in which files/data of websites are stored, and data files are used in MySQL:

How to defend yourself?
One vulnerable machine on the network is sometimes enough to infect all connected systems and servers. Given the risks to operations, reputation and profit, companies should take the initiative in eliminating such threats. Recommendations for risk reduction include:
- Backing Up Important Files
- Disabling or minimizing the number of third-party or unverified repositories
- The application of the principle of least privileges
- Updating server software and terminals (or using virtual patches)
- Regular network monitoring
- Checking event logs to detect intrusion or infection symptoms
Hash functions SHA256 RANSOM_ELFEREBUS.A:
0b7996bca486575be15e68dba7cbd802b1e5f90436ba23f802da66292c8a055f
D889734783273b7158deeae6cf804a6be99c3a5353d94225a4dbe92caf3a3d48





